How to use cryptography to verify Scope 3 emissions
Decoding the intersection of privacy-preserving cryptography and the heavy power demands of the intelligence age
2/4/2026
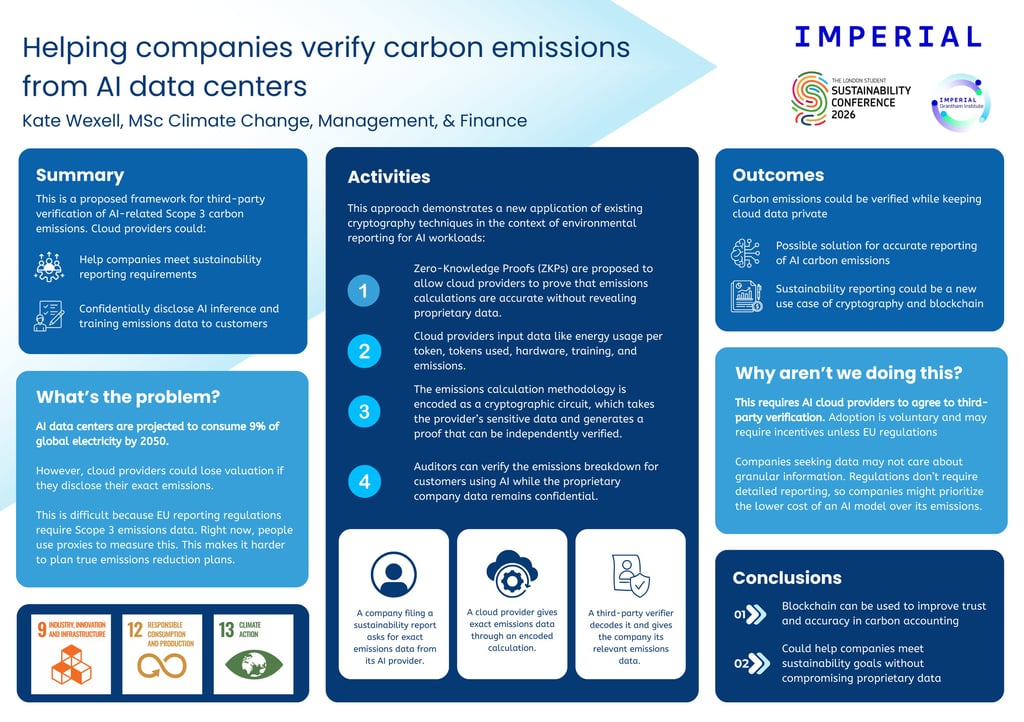
The AI boom is no longer just a Silicon Valley success story. By 2050, data centers are projected to consume roughly 9% of global electricity.
The battle for leadership in AI is inextricably linked to the battle for leadership in energy. But as we construct this infrastructure, we’ve hit a wall in transparency.
In the world of climate finance and corporate governance, we are seeing a massive shift toward accountability. Regulations like the EU Corporate Sustainability Reporting Directive (CSRD) are no longer “nice-to-haves.”
They are mandates requiring companies operating in the European Union to disclose Scope 3 emissions: the indirect emissions that occur in a company’s value chain. For any firm leveraging AI, those Scope 3 numbers are exploding.
The problem is that cloud providers treat their energy data like a state secret. Sharing granular energy usage could impact company valuations or reveal proprietary operational efficiencies. For example, if an AI company has a less efficient use of energy, this could signal a worse model and tank their valuation.
So this develops a paradox: we need to hit net-zero goals, but have limited data about the environmental impact of data centers.
Currently, carbon accounting is a game of averages. Most tools rely on proxies guessing the emissions of AI because they lack direct access to the “black box” of the data center.
If you don’t know the exact energy intensity of your AI training or inference, you can’t accurately report your impact, and you certainly can’t select models based on their environmental efficiency.
That’s why I’m presenting this framework as a potential solution at a research conference in London later this month.
Solving the trust gap with cryptography
The most effective levers in climate policy are often those that correct market failures by improving the risk-return profile of an investment. In this case, the market failure is a lack of data.
The novel approach involves applying Zero-Knowledge Proofs (ZKPs) or ZK-SNARK protocols to carbon accounting. For the uninitiated, ZKPs allow one party (the cloud provider) to prove to another (the auditor or customer) that a statement is true without revealing the underlying data itself.
Here’s how it works:
The methodology for calculating emissions is encoded as a cryptographic circuit. This would be a formula that calculates emissions based on data about hardware, token usage, energy intensity, and other variables.
The cloud provider inputs this sensitive data into the circuit.
The system generates a proof that the emissions figure is accurate based on the agreed-upon methodology. Essentially, this is an encryption that contains the data but cannot be opened.
This is sent to the customer and allows them to hand an auditor a “verified SCI score” (Software Carbon Intensity) without ever seeing the proprietary operational data of the cloud provider.
It provides a secure method of transmitting information without risking a cloud provider’s valuation.
Why isn’t this everywhere?
If this has the potential to accurately communicate emissions data for reporting, why isn’t it already in practice?
Most importantly, it requires AI cloud providers to agree to third-party verification. Adoption is voluntary and provides no financial incentive. The only way to ensure compliance is to offer a profit-sharing mechanism between the verifier and cloud provider, or for EU regulations to tighten. Stringent policy restrictions may force cloud providers to comply.
Additionally, companies seeking data might not care about granular information. Current policies do not mandate exact data, so proxies suffice. As customers are choosing their enterprise AI model, they may also prioritize pricing over emissions.